According to Brandwatch, people have on average 7.6 social media accounts. This is a useful statistic to keep in mind when you’re digging into social media profiles. During an investigation, it’s not uncommon to encounter closed accounts. You might deal with this by searching for friends and family members to find information but, as an alternative, you can search for other social media accounts owned by your target. Ideally, you should do both but in this quick tutorial, I will focus on the latter.
Assuming that we already know the username(s) of our target, I will show you three different but very similar tools with which you can trace your target across multiple social media platforms.
It is important to stress that tools like these will not find the needle in the haystack for you – they just save you lots of time, which in turn can be used for other tasks, such as the actual analysis of all the information collected.
In total, I’ve selected three tools that I recently have come across on Twitter and the web:
Please note that this list is not exhaustive and if you know any other tools – let us know on Twitter using the #OSINTCurious or in the comments section below!
There is a 10 Minute Tip video that shows how to use some of the tools and sites mentioned below.
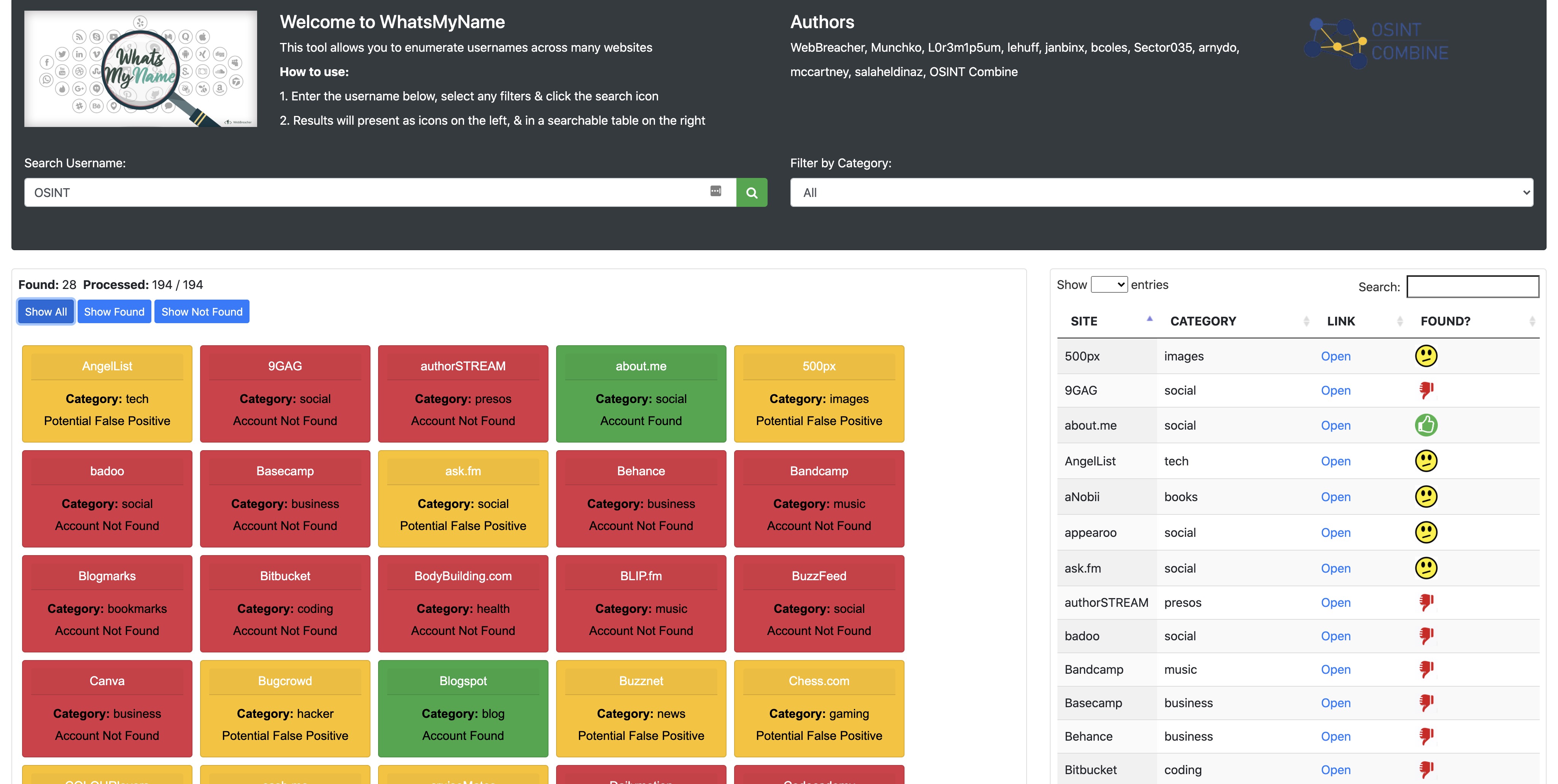
WhatsMyName Web App
The first tool I want to highlight is WhatsMyName. In particular, I want to show you the web application that OSINT Combine has developed in collaboration with the original author, Micah (@webbreacher), and other contributors of WhatsMyName. The interface is super easy to use and doesn’t need further explanation. Simply copy the username and paste it into the search bar. To refine your searches, you can select a category on the right side of the interface. For example, if you know that your target is a gamer, you may want to check gaming sites first and then the rest. Generally, I recommend going for ‘All‘ as you may find interesting leads. Just a week ago, I was searching for a person and to my surprise, I’ve found interesting information on a chess forum – something I would have never expected from the user.
In its original form, WhatsMyName is Python-based. The GitHub repository of WhatsMyName can be accessed here. It has been since integrated into several other OSINT tools, such as Spiderfoot, Recon-NG and Sn0int. For a quick how-to with Spiderfoot, check out this new tutorial. And for a quick 10-minute OSINT tip with Recon-NG, check out our video.
Namecheckup.com
The next tool is Namecheckup. It was actually built to allow users to check the availability of social media usernames and domain names across many platforms. Nevertheless, it’s a great tool that perfectly fits our investigative needs.
The website has a nice interface, it’s super easy to use and doesn’t need any explaining. To demonstrate its viability and highlight a common challenge, here’s a quick example with the UK’s prime minister, Boris Johnson (BorisJohnson – see Figure 1).
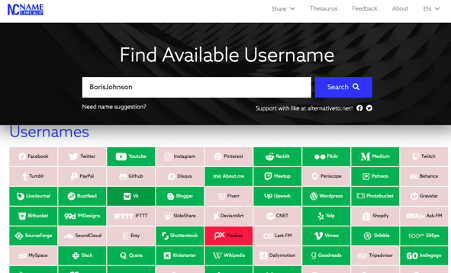
For our purposes, we are only interested in the grey coloured boxes – these are the ones where the username is taken. As a next step you would have to verify the account. To do so, simply click on a greyed box of interest and proceed with your verification steps.
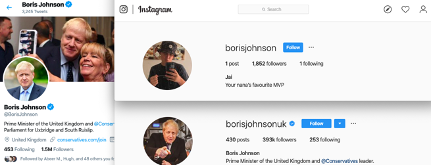
Coming back to Boris Johnson, the suggested Twitter account was correctly identified (Figure 2); however, the suggested Instagram account is not Boris’s account (see Figure 2). This is something you will probably often see. In this case, try change the username and repeat the search. Or, go directly to the platform of interest and search for him or her, using different usernames as well as the real name. In this case, I decided to go directly on Instagram and search for Boris Johnson, which eventually gave me his correct account (Figure 2).
Refining your searches is a normal and important process. If you don’t have a single hit, it does not necessarily mean your target is not on social media. He or she might use a username which is totally different than the actual name.
Sherlock
The last tool I want to demonstrate is Sherlock, which is provided by the Sherlock Project. Similar to UserRecon, Sherlocks allows you to easily trace users across many platforms. In fact, at the time of writing this blog post, Sherlock covers 306 social media platforms. It is a very powerful Python-based command line tool, which is also actively maintained by its developers. If you don’t know much about your target, I highly recommend Sherlock as it covers a large number of platforms and you might find relevant information on social media platforms other than the usual big ones that come to mind, such as Facebook, Instagram, TikTok & Co.
Sherlock is easy to use and doesn’t need much explaining. To install it, simply follow the steps on the GitHub page. Nevertheless, there are two things that I’d like to highlight:
First, you can trace multiple usernames across all platforms. This is particularly useful when dealing with multiple targets or trying different variations of a single username. To do so, just add the usernames separated by a s space to the end of the command. So, for example:
Python3 sherlock.py lorandbodo dutch_osintguy technisette
If you want to conduct your searches under high OPSEC, Sherlock has got you covered, too. You can make requests over a proxy, a list of proxies and even the TOR network. For more information go check out the GitHub page.
That’s it for today! Thanks for reading this blog post and if you like to share other tools and strategies on how to trace usernames across the web, please do so on Twitter, using #OSINTCurious, comment below, or reach out to me @LorandBodo!

