Hi my name is Josh, I’m an OSINT analyst for the financial industry, digital forensics analyst, and former private investigator. I remember the day I realized that I wanted to get into information security and ultimately became OSINT curious.
This story goes back to my management days of running a helpdesk for a retail chain. One of my workers told me there was an upset customer on the line who was demanding to speak to a manager. The phone conversation went something like this:
Me: Hi this is Josh, how can I help?
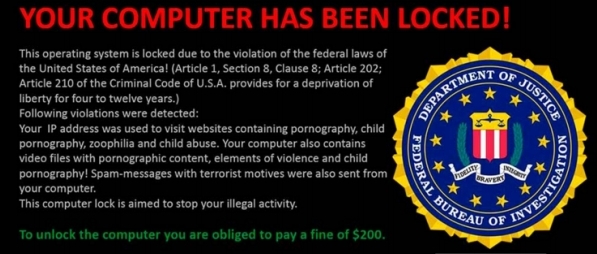
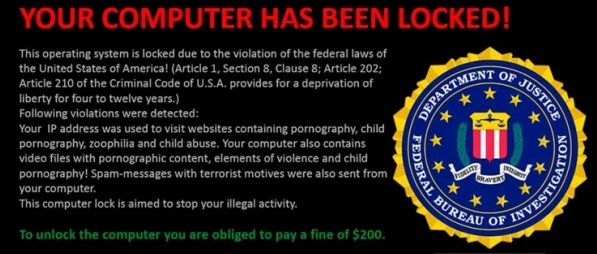
Customer: Yeah I got this damn warning on my computer that’s saying the FBI is coming to arrest me!
Me: Ok sir, are you near you computer so you can read to me what you are seeing?
Customer: Yeah this is what my computer says “This CPU is blocked for one of the following reasons: Copyright violations… thats bullsh**! Child pornography… that’s bullsh**! And zoophilia… whatever the hell that is… that’s bullsh** too!”
With a smile, I fought back laughter and asked the customer if I could place him on hold for a second to look something up . A quick search online showed me that this person had a common malware infection known as the FBI Moneypak ransomware.
The ransomware info itself wasn’t the only thing I found when searching the Moneypak scam. I also found a blog from a researcher at Kaspersky Lab who was explaining the Microsoft Tech support scammers.
This blog was different though. The researcher didn’t just warn people of the scam. He engaged the scammers in his virtual machine with the goal of learning what the scam actually was and who these scammers were. The researcher logged everything along the way and took screenshots that explained his technique. This blog took you on a journey of trying to unmask the scammers.
I read it start to finish… twice, then I printed it out to show some of my co-workers. “Check this out!” I said as I showed it to my friends and my wife later that night. Some people thought it was cool, but I thought this research was badass! Learning the badguy’s techniques and outsmarting them to help others avoid falling prey to thier scammer tactics was something I wanted to learn more about.
The events of that day started a learning journey that lead to research, studies, and infosec networking. Eventually I started blogging and teaching about what I was learning in the OSINT field and that path would be what got me to where I am professionally today. So thank you ransomware jerks!
I am Baywolf88 on Twitter and I’m looking forward to contributing with the community here.