When it comes to IoT or other online devices, there are quite a lot of options to investigate them. It is possible that you are working as a penetration tester that needs some information on a client, but also an investigator that is looking into online activity can use some of these skills. Why might it be a good idea to look at an IP address via Shodan or Censys, and how could they help you in an investigation? In this article we’ll go over some use cases and show how they might be able to propel an investigation forwards or investigate a digital component like a webserver. To be able to use most of the filters that are explained in this blog post, you will need to register an account. And even the free account will give you access to some helpful filters already.
IP addresses
When you have an IP address that you need to investigate, a lot of people simply check them via a Whois query, or run them through a website like ipinfo.io and leave it at that. When it turns out to be a home router there usually isn’t a lot of information to gain so that’s where they stop. But it’s always a good idea to at least have a look within Shodan or Censys to see what they’ve scanned on that IP address, or even the netblock it is part of. Especially when you’re looking into a company.
Within Shodan and Censys you can query a single IP address, and get information on that single address as shown here. This is the IP address belonging to the URL https://stellar.mit.edu and when opening the link to the information page, we see it is located in netblock AS3. A netblock is a range of consecutive IP addresses that are appointed to a party, in this case MIT.

If you are interested to find out what else is on the network of that company, you can check out what IP addresses they own, or which netblocks they are assigned, and you can query them. To search for all IP addresses in the range 18.9.47.0 up to 18.9.47.255, you can search in two ways. Simply as a range of IP addresses, like this:
ip:18.9.47.0-18.9.47.255
Or you can use the ‘CIDR’ notation, that is the common notation to write netblocks or IP ranges. But if you aren’t familiar with CIDR notation, the previous notation will give the same results:
net:18.9.47.0/24
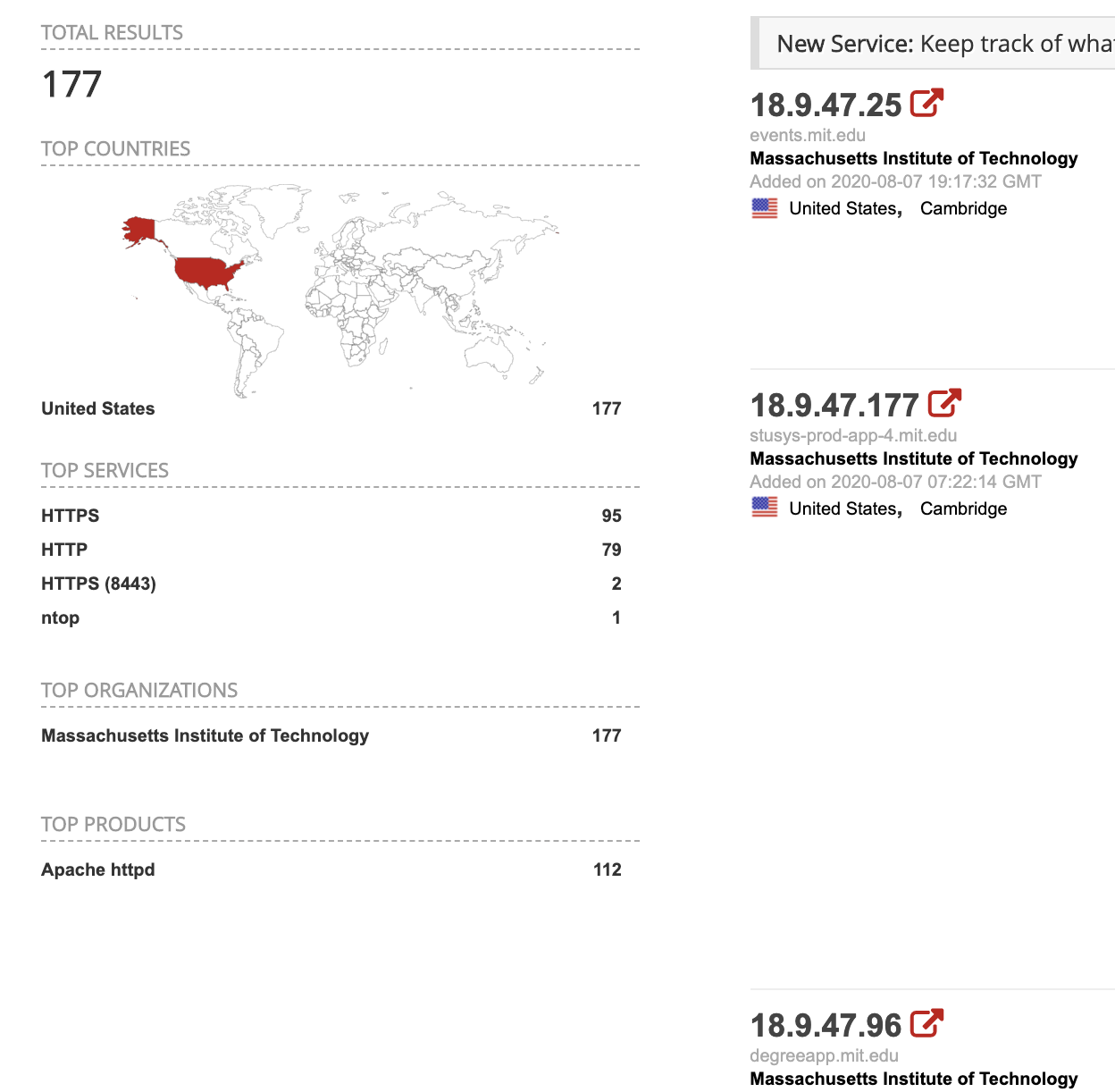
Searching in this way will return many more IP addresses that might be of interested when you are investigating a company. Because it is not uncommon to get several hundreds hits, exposing websites that you might not have been able to find with a simple Google search.
Certificates
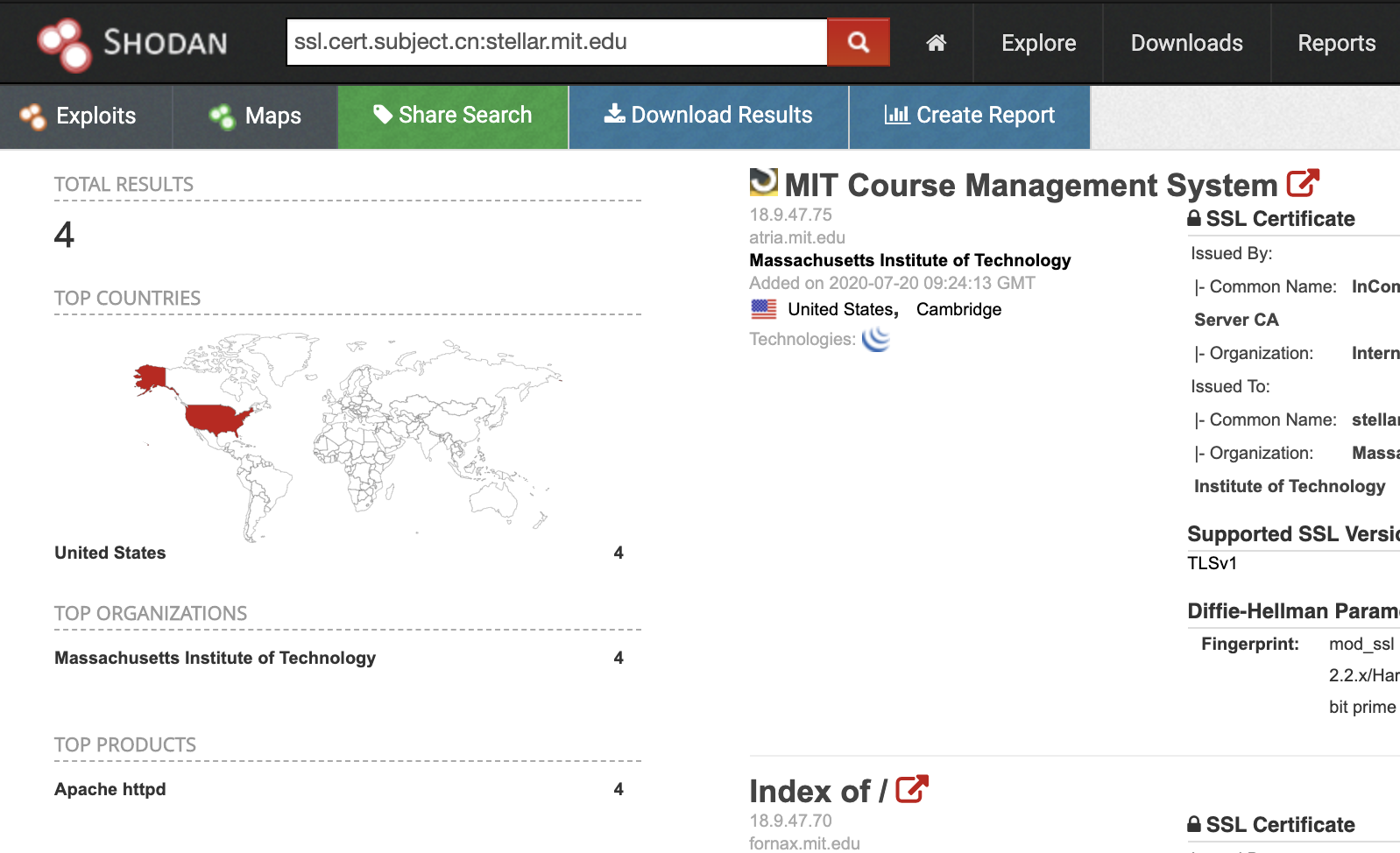
When you have a URL, you can put it into the Shodan search bar and find out all servers that have that URL somewhere in the source code (yes, Shodan also saves the raw pages). But you can dive a bit deeper by specifically searching for servers that served the digital certificate (the little padlock in the address bar) that contained that specific URL. To get those results there is the filter ‘ssl.cert.subject.cn‘. This filter looks in the database for SSL certificates where the subject canonical name, or cname, is that URL:
ssl.cert.subject.cn:stellar.mit.edu
Instead of finding 11 servers on the internet that have the part ‘stellar.mit.edu’ within the URL or the information sent out by the server, it seems only four IP addresses actually serve that specific digital certificate. So you now know where to focus on during an investigation.
Headers and HTML
Shodan also has a function that is similar to the Google search option ‘intitle‘. But since Shodan scans IP addresses, and not URL’s, it will return the systems by IP address and thus exposing the actual IP address of a system and sometimes bypassing any kind of DDoS protection they have in place. To look for page titles this way, search with the directive ‘http.title‘, like this:
http.title:"Massachusetts Institute of Technology"
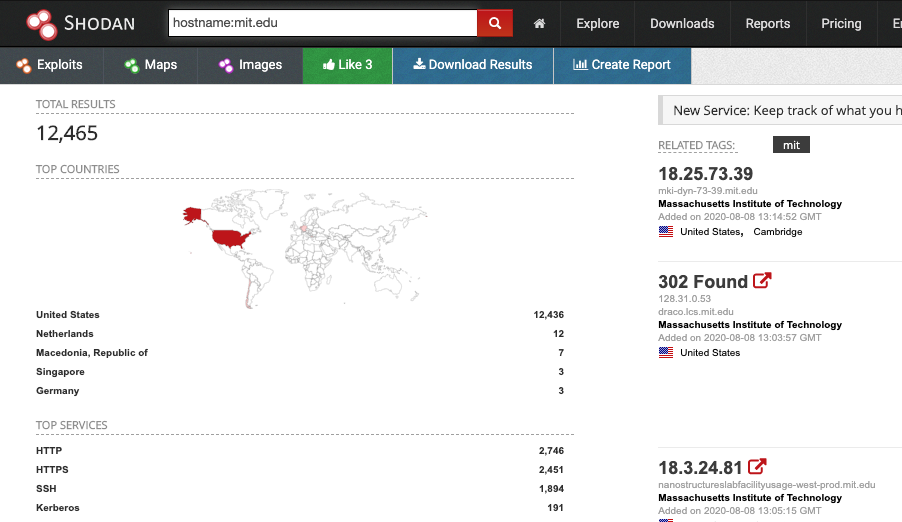
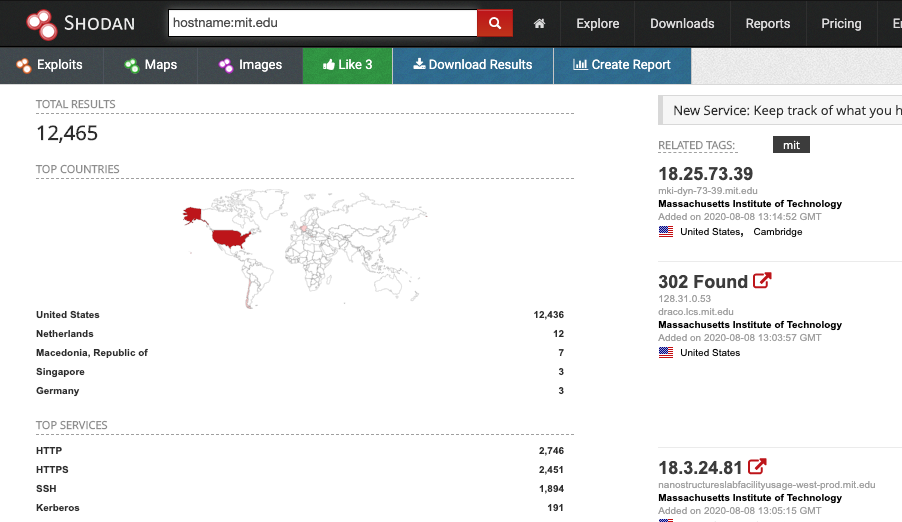
And another way of searching for specific webservers, is by using the filter option ‘hostname‘ to find devices that listen to a specific URL. So to find even more interesting web servers in use by MIT, you can search for those URL’s in the following way, resulting in a whole bunch of servers that are online:
hostname:mit.edu
Another search option is ‘http.html‘ that gives you the option to search within the source code of the page at the moment it was scanned by Shodan. This can even be used to search for Google Analytics codes, for instance to find even more MIT webservers, especially the ones that don’t use the URL’s or the certificates you’ve searched for in the earlier steps:
http.html:'ua-1592615'
It may not give as many results as a good reverse analytics tool, but that is to be expected, because not all webservers or proxy servers will present a webpage when you use an IP address without sending a URL in the header.
Webcams & IoT
When you are investigating a domain name or the associated IP addresses for a company, it doesn’t hurt to search within Shodan for any screenshots of publicly available webcams, by using the filter screenshot.label in conjunction with other filters. For instance, you can target your query to search for devices within AS45102 (the ASN of Alibaba). With the more expensive enterprise account, it is even possible to search by ‘tags’, but for the free account this is one of the ways to find open webcams that are labelled:
screenshot.label:webcam asn:AS45102
And maybe you are lucky and you are investigating a small company that exposed a webcam, and give you the opportunity to find more information, or pivot from there to Google Street View.

Tips
Search engines like Shodan are not only for IoT devices, unlike some people think. Anything that is connected to the internet and is able to be indexed by a service like this can be interesting for an investigator. Of course it depends on what you are investigating, but when it comes to companies with an online presence, it may be a good idea to check what might be out there.
A new frontend for Shodan has also been launched some time ago, called https://beta.shodan.io/. It works pretty much the same, but it actually shows historical information about the scanned IP addresses and services.
For an overview that is available in the free version, after creating an account, here is a small list of filters.
| ip:111.222.111.222 | Show information on a specific IP address or a range of addresses |
| net:111.222.111.0/24 | Display indexed IP addresses within a netblock |
| asn:AS12345 | Filter devices on the ASN that they are part of |
| hostname:website.tld | Find for devices that handle a specific URL |
| http.html:sourcecode | Find servers that have a specific source code in their HTML |
| http.component:apache | Search for devices that run a specific technology, like: Apache, jQuery, PHP etc |
| has_screenshot:true | Filter on indexed devices that have a screenshot captured by Shodan. This can only be ‘true’ or ‘false’. |
| screenshot.label:name | Find screenshots that are labelled with: desktop, ics, login, loggedin, pos, screensaver, terminal, webcam or windows |
After creating an account, I would recommend to play around with Shodan. And I would absolutely recommend to grab the lifetime membership that can be found on the page after logging in, or you can wait for their almost yearly Black Friday deals. This will give you access to even more queries per month but also have access to:
https://maps.shodan.io/ – An interactive map with the indexed devices plotted by their approximate location.
https://images.shodan.io/ – An overview of screenshots captured by the Shodan crawlers.
https://exploits.shodan.io/ – Searching for exploits that have been identified by Shodan.
And to make it even easier, it is even possible to query Shodan directly from your browser. Simply download the extension for Google Chrome, or the add-on for Firefox.